Frequently Asked Questions
Why do you publish such a dangerous tool? Don't you think threat sources could use it to exfiltrate data from my organization?
Yes, like any other penetration test tool (find here a starting point to find other pentest tools), threat sources could use it to perform attacks. If you have sensitive data, do not connect your information system to the Internet, do not add a DNS resolver connected to the Internet in your information system. Finally, use this ethical-hacking tool to check that you are protected.
Do I need to "root" my device before using VPN-over-DNS, like with many other VPN applications?
No.
Why should I download VPN-over-DNS, since when I connect my device to an open Wi-Fi network, I already get Internet access?
Open Wi-Fi networks are not systematically free hotspots: they do not systematically connect you to the Internet. Often, they redirect you to a captive portal, asking for a corporate login/password to connect to internal resources, or a Visa or Master Card Number, before connecting to the Internet.
Do you mean that with VPN-over-DNS, I will be able to connect to Wi-Fi networks protected by a WEP (or WPA) private key?
No. To connect your device to a Wi-Fi network protected by a WEP (or WPA) private key, you will always need to know the key. VPN-over-DNS can work on such a network, but you need to enter the key when you first connect to the Access Point.
Where can I find open Wi-Fi networks, protected by captive portals?
Hostels, airports, train stations, Internet services providers (xDSL boxes) often provide such open networks. Sometimes, companies also do it on their main offices. You must check that you are allowed to use these networks before trying to set up any kind of tunnel through them. For instance, you may be a customer of the Internet service provider that offers this Wi-Fi network, and you do not want to waste time entering your credentials each time you connect to their captive portal. In such a case, and depending on your ISP policy, you may be allowed to use a tunnel on top of their network. The same way, if you are a customer of the hostel, you may be allowed to set up a tunnel on top of their Wi-Fi infrastructure. This is your responsability to check those prerequisites before setting up the tunnel.
In the past, I have always prefered buying a data plan when I travel in a foreign country, this way I can connect from everywhere without having to set up a DNS tunnel. What should I do now?
Buy a data plan.
If I am not authorized to set up a DNS tunnel, what complementary usages could be of interest for me?
Password cracking software (like JohnTheRipper) lets you know if your password is safe enough. WEP key cracking software lets you know if your WEP key is secured enough. The same way, VPN-over-DNS can be used as a proof of concept, letting you know if your network is safe enough, or if your next generation firewall can correlate DNS queries to detect and filter tunnels, without affecting normal DNS queries. This will help you improve your network security.
Before installing VPN-over-DNS, how can I check that I could set up a DNS tunnel on top of a specific Wi-Fi network I can already connect to, but that does not seem to be connected to the Internet?
Just try to ping the host www.vpnoverdns.com. You will get a timeout since your network is not directly connected to the Internet, but if the IP address 149.202.53.208 is displayed, it means that your DNS resolver is connected to the Internet. So, you could certainly get Internet connectivity through DNS tunneling on this network.
Can I make DNS tunneling with my laptop running Windows?
Yes. Just click here to get the VPN-over-DNS Value Pack for Windows.
Can I make DNS tunneling with my laptop running Mac OS X?
Yes. Just click here to get the VPN-over-DNS Value Pack for Mac OS X.
Why do I need to install Adobe AIR ™ to use VPN-over-DNS?
VPN-over-DNS is an Adobe Flex © application, written with Action Script code (for the GUI) and Java libraries (for network interaction). Adobe AIR ™ is a runtime mandatory to run the Action Script code.
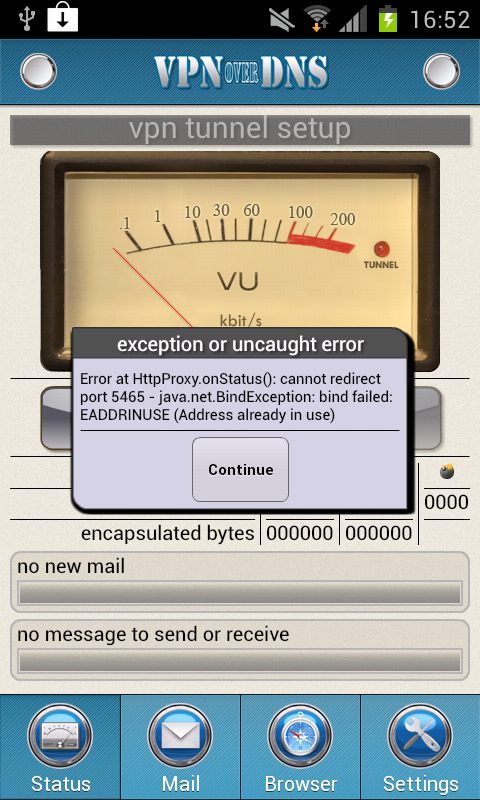
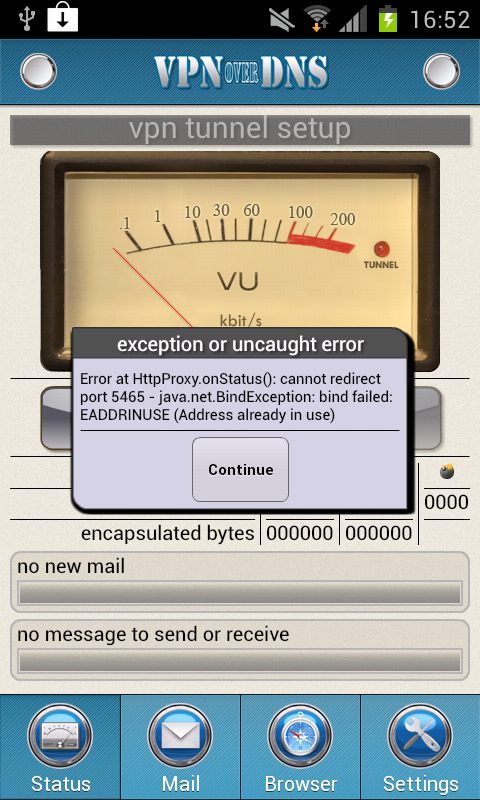
I get a pop-up complaining about an exception: "Address already in use". What does this mean?
Either you started VPN-over-DNS twice, so the last instance has had an error when trying to redirect ports that are already redirected by the first instance. In that case, kill every instances of VPN-over-DNS and start only one at the same time.
Or you already have a running task or background service that locks a specific port also used by VPN-over-DNS. For instance, Kies Air on Samsung devices locks the port TCP/8080. In such a case, close the Kies Air application before launching VPN-over-DNS.
Why have you implemented a Mail User Agent and a basic web browser in the application? This does not meet my needs since I would have prefered to use the same Mail User Agent and web browsers I use ordinarily.
You can use any Mail User Agent or web browser, with the port redirection feature of VPN-over-DNS. They will often be slower than the ones integrated in the application. It is only a matter of choice, for you.
Why do I need full Internet connectivity to log in the application or to save my mail provider credentials?
Logging in the application or saving your mail provider credentials is a process during which you exchange sensitive informations with our server farm. To protect those informations and credentials, we do not use DNS tunneling but a secured SSL/TLS channel. This is why you need a full Internet connection to log in the application or save your mail provider credentials.
Users need full Internet connectivity to log in the application. But when I need to use the application, I do not have full Internet connectivity. So, how can it work?
Do not tap on the "Log out" button in the application, before you stop it, if you have no reason to. Then, you will not have to "log in" again when you later start the application. Logging out of the application should only be done when you want to connect to another VPN account. Moreover, if you do not have Internet connectivity, you will also be able to connect to the previous account you were logged in, since the last credentials used to log in are locally cached by the application.
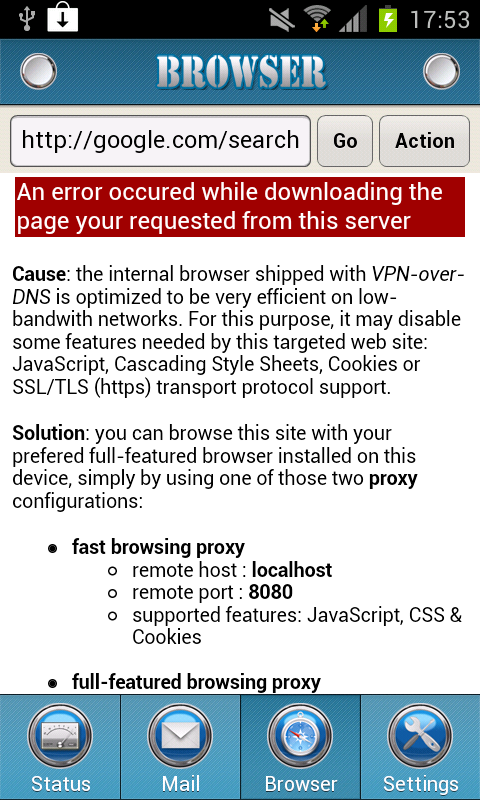
Sometimes, I get the following error message, while browsing a web site. What does this mean and what can I do?
Some features, mandatory by the site you are trying to connect to, may not be available by the VPN-over-DNS native browser. Follow the instructions to use an external browser to connect to the site.
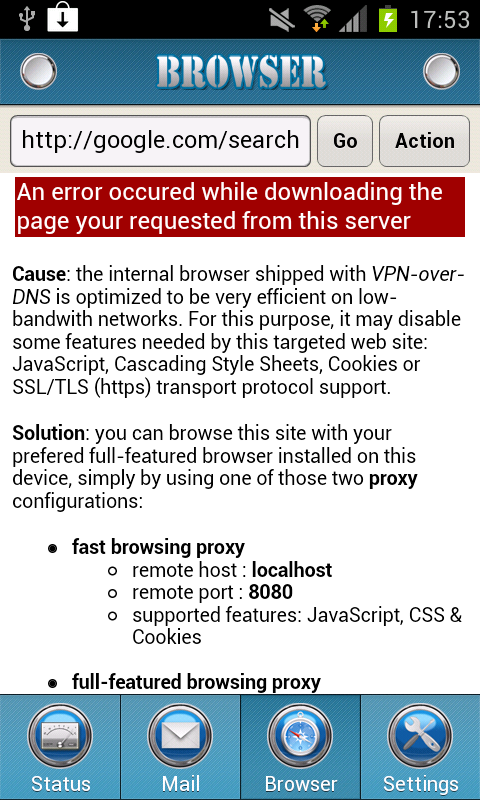
Google does not seem to work with VPN-over-DNS, what the f*ck?
The native VPN-over-DNS browser works very well with Bing, a well-known search engine by Microsoft, that works with any browser. This is why our VPN client home page is Bing. On the contrary, supporting Cookies is mandatory to use the Google search engine. Since the native browser does not support Cookies, you can not use it to search with Google, you are encouraged to use Bing. Don't panic: this does not mean you cannot access Google with VPN-over-DNS ! It simply means that to do so, you will need to use the port redirection feature instead of simply using the VPN-over-DNS internal browser (see the specific port redirection section in the documentation, for this purpose).
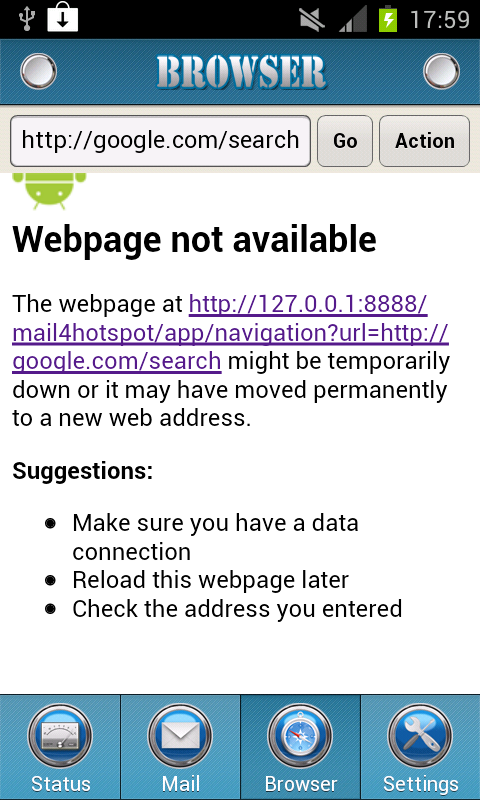
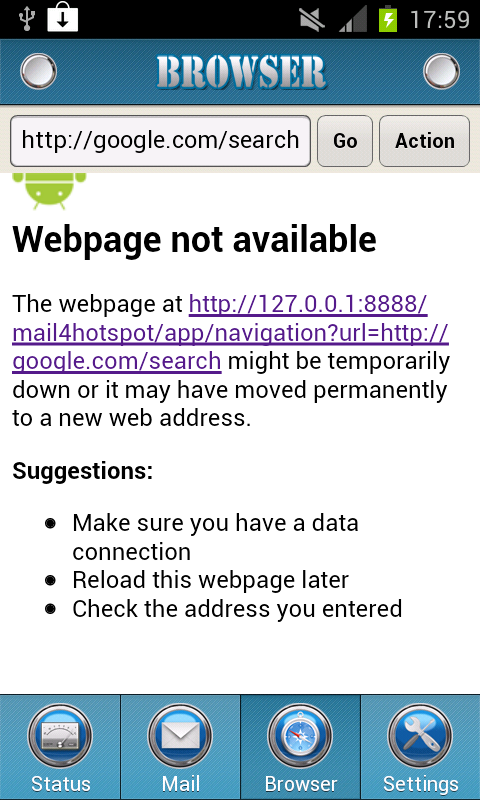
Sometimes, I get the following error message, while trying to start a web session. What does this mean and what can I do?
This error page means the native browser was unable to set up the DNS tunnel. This simply means that you are not connected to any network with which such a tunnel could be set up. Often, this means you have just been disconnected from your Wi-Fi network, because of a lack of signal strength.
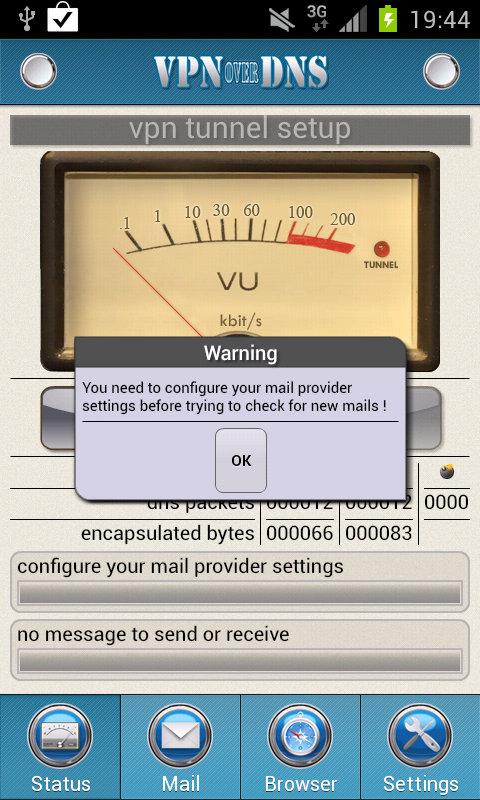
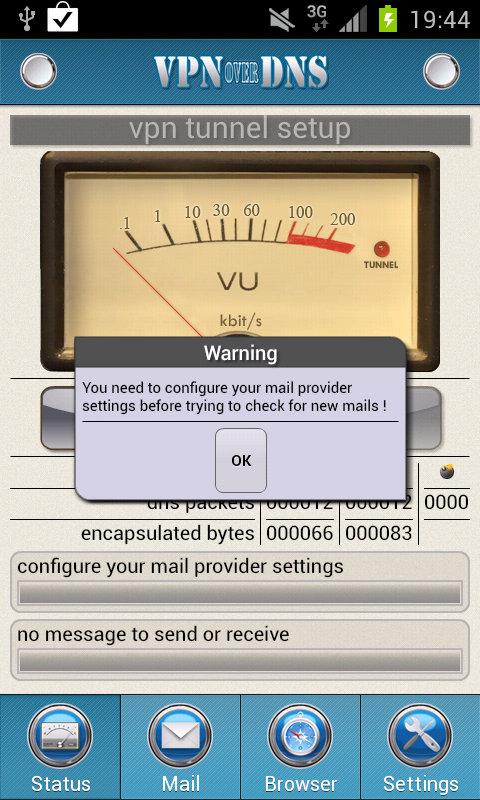
I do not want to configure my mail provider credentials, since I only want to use VPN-over-DNS to browse the Internet (in fact, I do not want to inform you about my Google mail credentials, no way !). But each time I try to set up the tunnel, it fails with the following pop up, asking me to configure my mail. How can I use VPN-over-DNS without configuring my mail provider credentials?
No problem, you can use VPN-over-DNS without configuring your mail. Simply, do not tap on "Start" on the status screen: tapping "Start" is the way to set up the tunnel specifically to connect to your mail provider. When you browse Internet or use TCP port redirection, even by means of an external browser or another application, the tunnel is automatically started by VPN-over-DNS, you never have to set it up manually.
My mail provider is not in the list of the four only providers supported by VPN-over-DNS : GMail, HotMail/Live, Yahoo! Mail and FastMail. How can I get my mail?
In such a case, you have three possibilities to get your mails. Either you redirect your mails from your main mail provider to a new account you create on GMail, for instance, and you configure this new account in VPN-over-DNS. Or you use VPN-over-DNS to tunnel an external browser (Chrome for instance) to the Internet, and you use this browser to access the web mail provided by your mail provider. Or finally you configure VPN-over-DNS to tunnel IMAPs/POP3s/SMTPs to your mail provider, and you configure any Mail User Agent installed on your device to use those TCP port redirections.
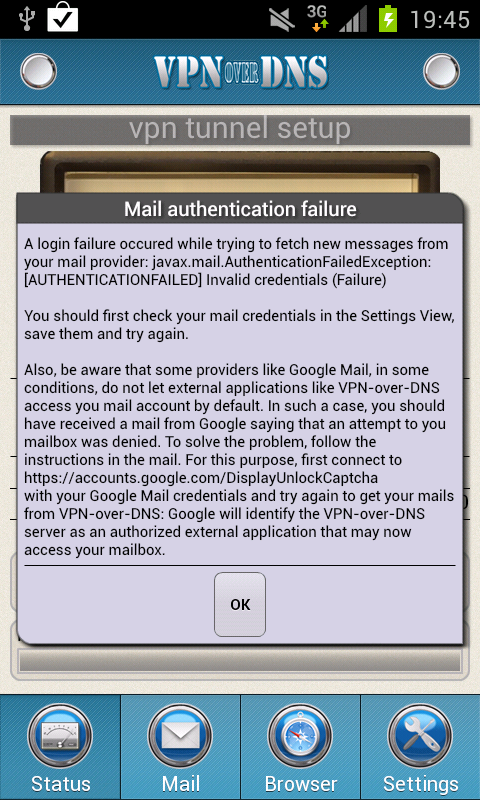
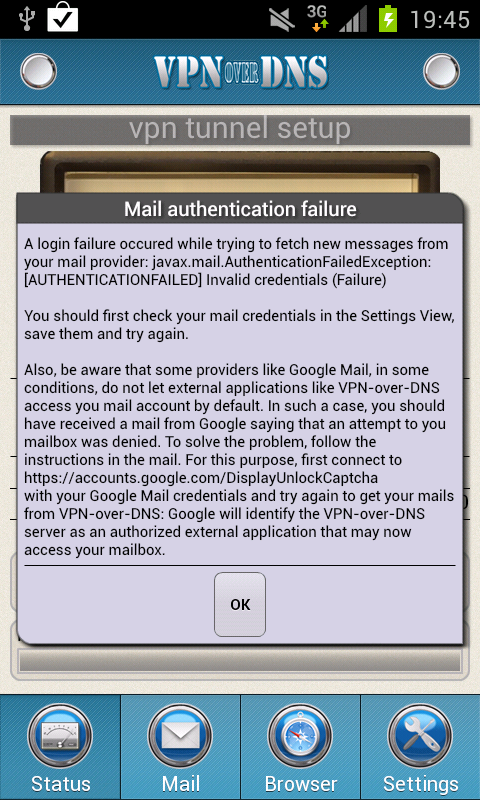
I checked my mail credentials three times, they are correct but I always see this pop up complaining about an authentication failure. What is the problem and what can I do?
First, read carefully the pop up content, not only the header, and follow the instructions: you are certainly using a mail provider like Google Mail, that needs you to explicitely authorize external applications like the VPN-over-DNS server farm before letting those servers access your mailbox. Thus, you should have received a mail from your provider Google saying that an attempt to connect to your mailbox was denied. To solve the problem, follow the instructions in the mail. For this purpose, first connect to the following URL
https://accounts.google.com/DisplayUnlockCaptcha
with your Google Mail credentials and immediately try again to get your mails from VPN-over-DNS : Google will then identify the VPN-over-DNS server farm as an authorized external application that is now allowed to access your mailbox.
I've heard that IODINE is available on Android, so what are the main differences between IODINE and VPN-over-DNS? Also, what about DNS2TCP?
IODINE, an excellent piece of software by Bjorn Andersson & Erik Ekman, packaged for Android by Collin R. Mulliner, is totally free, like VPN-over-DNS. With IODINE, you need to install the server yourself (be prepared to get two distincts IP addresses, one for your BIND instance, the other for IODINE: they should not use the same IP address on production environments, since IODINE DNS forwarding is not totally transparent). With VPN-over-DNS, you do not need to install the server: the application is shipped with a VPN account to connect to our VPN server farm. IODINE is based on tunneling IP datagrams over DNS queries. On the contrary, VPN-over-DNS is based on a specific implementation of the Mail User Agent and the browser, inside the application, and on TCP port redirection for external clients. This way, VPN-over-DNS is much more like DNS2TCP (the TCP over DNS implementation made by Olivier Dembour and Nicolas Collignon) than like IODINE, but DNS2TCP is not available on Android.
What are the other products available for DNS tunneling with an Android device?
On the Android platform, there are currently six products for this purpose: IODINE, AndIodine, Element53, MagicTunnel, SoftEther, and VPN-over-DNS. Element53, an application by Sander Nijhof and Marcel, is a way to get a TCP-tunnel to a socks proxy server. They provide a publicly available socks over DNS server for this purpose. MagicTunnel is based on IODINE and implements IP over DNS. Let us know if you have more informations about other similar products.
Can I make DNS tunneling with my iPad or my iPhone device?
Yes. VPN-over-DNS, running on your Android device, can share the VPN-over-DNS web proxies to your iPad or your laptop: just connect your iPad or your laptop to the same local Wi-Fi network (for instance, the one with the captive portal you want to bypass), and configure the proxy of your iPad or laptop to the IP of your Android device, and to port 8080 or 8081 depending of the proxy you prefer.